Tailscale
Tailscale
This integration guide is community supported. It's not guaranteed to be complete, accurate, or up-to-date. It's likely that if this integration guide does not work for you that changes occurred with a third-party application.
Important Note: This documentation is version specific. Make sure you check the section outlining the tested versions.
Important Note: We always recommend users read the third-party documentation as part of the integration process to ensure configuration elements matches their needs. As such the See Also section is likely to have important links.
Important Note: If you find an error in this documentation please make a Pull Request, start a Discussion, or contact us on a Chat Room.
Tested Versions
Before You Begin
Important Reading
This section contains important elements that you should carefully consider before configuration of an OpenID Connect 1.0 Registered Client.
Common Notes
- The OpenID Connect 1.0
client_idparameter:- This must be a unique value for every client.
- The value used in this guide is merely for readability and demonstration purposes and you should not use this value in production and should instead utilize the How do I generate a client identifier or client secret? FAQ. We recommend 64 random characters but you can use any arbitrary value that meets the other criteria.
- This must only contain RFC3986 Unreserved Characters.
- This must be no more than 100 characters in length.
- The OpenID Connect 1.0
client_secretparameter:- The value used in this guide is merely for demonstration purposes and you should absolutely not use this value in production and should instead utilize the How do I generate a client identifier or client secret? FAQ.
- This string may be stored as plaintext in the Authelia configuration but this behaviour is deprecated and is not guaranteed to be supported in the future. See the Plaintext guide for more information.
- When the secret is stored in hashed form in the Authelia configuration (heavily recommended), the cost of hashing can, if too great, cause timeouts for clients. See the Tuning the work factors guide for more information.
- The configuration example for Authelia:
- Only contains an example configuration for the client registration and you MUST also configure the required elements from the OpenID Connect 1.0 Provider Configuration guide.
- Only contains a small portion of all of the available options for a registered client and users may wish to configure portions that are not part of this guide or configure them differently, as such it’s important to both familiarize yourself with the other options available and the effect of each of the options configured in this section by looking at the OpenID Connect 1.0 Clients Configuration guide.
Assumptions
This example makes the following assumptions:
- Domain Root URL:
https://example.com - Authelia Root URL:
https://auth.example.com/ - Authelia Account:
user@example.com - Client ID:
tailscale - Client Secret:
insecure_secret
Some of the values presented in this guide can automatically be replaced with documentation variables.
Configuration
Authelia
The following YAML configuration is an example Authelia client configuration for use with Tailscale which will operate with the above example:
identity_providers:
oidc:
## The other portions of the mandatory OpenID Connect 1.0 configuration go here.
## See: https://www.authelia.com/c/oidc
clients:
- client_id: 'tailscale'
client_name: 'Tailscale'
client_secret: '$pbkdf2-sha512$310000$c8p78n7pUMln0jzvd4aK4Q$JNRBzwAo0ek5qKn50cFzzvE9RXV88h1wJn5KGiHrD0YKtZaR/nCb2CJPOsKaPK0hjf.9yHxzQGZziziccp6Yng' # The digest of 'insecure_secret'.
public: false
authorization_policy: 'two_factor'
require_pkce: false
pkce_challenge_method: ''
redirect_uris:
- 'https://login.tailscale.com/a/oauth_response'
scopes:
- 'openid'
- 'email'
- 'profile'
response_types:
- 'code'
grant_types:
- 'authorization_code'
access_token_signed_response_alg: 'none'
userinfo_signed_response_alg: 'none'
token_endpoint_auth_method: 'client_secret_basic'Application
To configure Tailscale to utilize Authelia as a OpenID Connect 1.0 Provider, you will need a public WebFinger reply for your domain (see RFC7033 Section 3.1) and point it to Authelia. The steps necessary are outlined in the Tailscale documentation on Custom OIDC providers KB article. This WebFinger reply is not generated by Authelia, so your external web server hosted at the root of your domain will need to generate the response (Check See also for example implementations). The following steps are necessary to get Tailscale working with Authelia:
- Your domain will need to reply to a WebFinger request for your Authelia account
- Your domain root is
example.comand the Authelia account in question isuser@example.comthe WebFinger request will be:https://example.com/.well-known/webfinger/?resource=acct:user@example.comthe complete request ishttps://example.com/.well-known/webfinger?rel=http%3A%2F%2Fopenid.net%2Fspecs%2Fconnect%2F1.0%2Fissuer&resource=acct%3Auser%40example.com - The WebFinger request needs to be answered with the following example reply:
{ "subject": "acct:user@example.com", "links": [{ "rel": "http://openid.net/specs/connect/1.0/issuer", "href": "https://auth.example.com" }] } - For any other users that you want to add to Tailscale, you will need to provide similar WebFinger replies (e.g. for
user2@example.comoruser3@example.com) - Once you have the WebFinger reply set up and your Authelia OpenID Connect Discovery endpoint is working (e.g.
https://auth.example.com/.well-known/openid-configuration), you can sign up for a new Tailnet (migration can only be done if the Tailnet is associated with a custom domain) via the link: Sign up with OIDC where you will see the following screen:
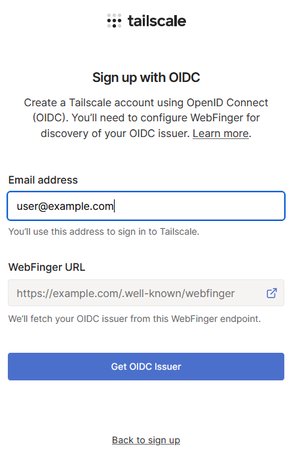
Note: Even though the WebFinger URL displayed ishttps://example.com/.well-known/webfinger, the actual GET request will be including request parameters, most importantlyresource. - After clicking on Get OIDC Issuer, Tailscale will fetch the WebFinger reply via
https://example.com/.well-known/webfinger/?resource=acct:user@example.comand follow the sethreftohttps://auth.example.com/.well-known/openid-configuration.
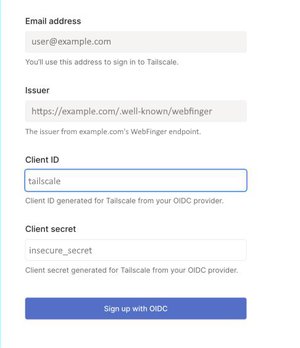
Note: Make sure that thehrefURL matches theissuerURL returned from the Authelia OIDC discovery endpoint - On the next screen you will need to add your client ID & secret configured in Authelia to finish the OIDC provider registration in Tailscale. See the following example screenshot:
See Also
- Tailscale Custom OIDC providers KB article
- RFC7033 Section 3.1 WebFinger: Identity Provider Discovery for OpenID Connect
- WebFinger example implementations